Check Point observes millions of Telegram channels being deleted
Check Point Software Technologies has documented the deletion of millions of suspicious Telegram channels. Around 20 percent of the blocked channels were linked to criminal activities such as the illegal trading of credit card and login data. However, cyber criminals remain active and quickly adapt their strategies.
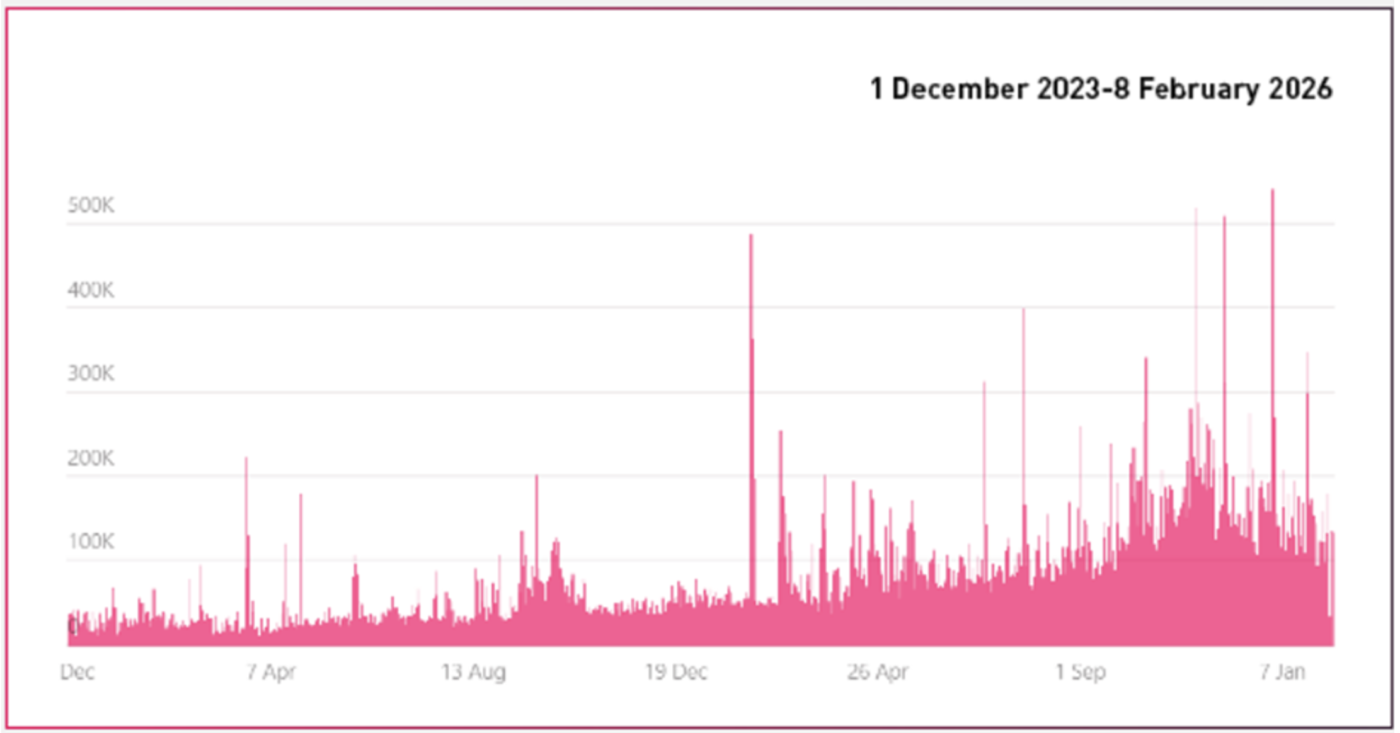
Check Point Software Technologies, a leading global provider of cybersecurity solutions, has observed a massive increase in the deletion of suspicious Telegram channels. In 2025, over 43.5 million channels and groups were blocked. Daily deactivations rose from 10,000 to 30,000 to 80,000 to 140,000 per day. On peak days, over 500,000 channels were even deactivated in a single day.
Telegram under increasing pressure
After years of pursuing a rather cautious moderation policy, Telegram recently came under heavy pressure. Following the arrest of CEO Pavel Durov in France at the end of 2024 and subsequent stricter moderation in 2025, the measures have now been significantly tightened. Automation, frequent blocking and more transparency led to record numbers of channel shutdowns.
According to Check Point Exposure Management, around 20 percent of the blocked channels were linked to criminal activities that directly affect companies. These include, in particular, the illegal trade in stolen credit card data and login information.

Criminals adapt quickly
However, an analysis by Check Point shows that the effects of the deletion actions are limited. Criminal groups do not simply disappear, but quickly reorganize themselves. Backup channels are often created before a shutdown, sometimes including a preloaded target group, so that the operation continues almost seamlessly after a shutdown.
In addition, thousands of forwarded messages continue to circulate, linking to blocked channels and keeping knowledge, data and instructions of cybercriminal methods alive in the scene. Data from Check Point shows spikes in forwarded messages linking to blocked sources, particularly during periods of high enforcement in February, March and April 2025, significantly extending the lifespan of criminal content even if the original sources are removed.
New circumvention strategies
Instead of leaving Telegram, attackers are developing new evasion strategies. These include «request to join» gating to exclude automated moderation bots, as well as disclaimers in channel bios, including tagging of Telegram managers to feign compliance. In addition, prepared backup structures are used to enable immediate reactivation after deactivation.
Despite brief experiments with alternative channels, Telegram remains the platform of choice. One prominent example is the Akula group, which temporarily switched to SimpleX at the beginning of 2025 but returned because the community did not follow suit to the extent required. Individual players use alternative apps for 1:1 communication, but Telegram remains the central location for outreach, recruitment and marketplace structures, i.e. trading in stolen information.
Continuous exposure management necessary
The raids on Telegram observed by Check Point are persistent and large-scale, but the cybercriminals' ability to adapt is also high. Shutting down conspicuous user accounts is still important. However, it is not enough to remove individual criminal channels - the underlying networks and structures must also be made visible.
Security teams that rely solely on enforcing platform policies run the risk of always being behind the curve. Those who invest in continuous exposure management and AI-supported threat intelligence can uncover the course of such operations and stop entire attack structures.
Further information can be found on the Website of Check Point Software Technologies.